In the winter of 2006, an affluent family returned home from their holiday vacation to find numerous billing statements from sources it had no history with. Further disclosure revealed that someone had se- cured three credit cards from three separate lending institutions, a pre-approval mortgage statement for a home they had no knowledge of, a significant cash withdrawal from one of their existing accounts and a change of address confirmation for their main account to an overseas address. After seeking immediate guidance, the family placed a freeze on all its accounts, filed a fraud alert with the three major credit bureaus, sent certified letters to each lending institution from which fraudulent credit was established advising that the applications that were submitted were initiated by an identity thief and filed a police report with the local agency. Subsequent to their meeting with their lending institution, they decided to remove all funds and place them with another institution disclosed only to the family attorney.
After a lengthy investigation, it was discovered that a trusted member of the household staff had sold the family's personal information, which included passwords, pin numbers and Social Security numbers to a third party who actually perpetrated the act. While the employee was later deported, the family never recovered the withdrawn funds and, to this day, remains emotionally scarred from this invasion of their life.
Understanding Identity Theft
Identity
theft is a criminal act committed by both skilled and unskilled thieves
with the mens rea(criminal intent) to replicate the victim's public
identity by extrapolating personal information from vulnerable sources
providing access to their wealth/credit through established records.
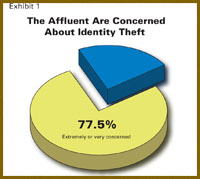
In a survey of 427 affluent individuals, slightly more than three-quarters of the affluent are extremely or very concerned about identity theft (Exhibit 1). Our experience indicates that more than ever the affluent community has become increasingly concerned with their risk to identity theft, from both media exposure and the personal experiences of family, friends and colleagues.
 What is very clear is that their wealth (regardless of public image)
and the manner in which their lifestyle communicates that wealth is at
the core of identity theft risk. Specifically, the greater the wealth
and the more people permitted access to the personal information, the
more likely identity theft will happen. Information such as bank
account information, wire information, residential addresses, Social
Security numbers, dates of births, telephone numbers, medical
information and real estate acquisitions were acquired and used to
deprive the wealthy of their identities and then their monies. Some of
the more common "leaks" include:
What is very clear is that their wealth (regardless of public image)
and the manner in which their lifestyle communicates that wealth is at
the core of identity theft risk. Specifically, the greater the wealth
and the more people permitted access to the personal information, the
more likely identity theft will happen. Information such as bank
account information, wire information, residential addresses, Social
Security numbers, dates of births, telephone numbers, medical
information and real estate acquisitions were acquired and used to
deprive the wealthy of their identities and then their monies. Some of
the more common "leaks" include:
Household staff that were not professionally screened
Travel agents, their staff and contractors
Residential contractors
Professional advisors, their staff and contractors
Family office executives and their staffs
Physicians and their staffs
House guests
Donation recipients
Galleries
Cyber trollers (who pose the greatest risk to the affluent community)
Tell Tale Signs: The Significant Seven
Preemptive
analyses of an affluent family's situation can, and often does, expose
"red flags" that identify when theft is a very real possibility. Many
times, we have found, after an assessment, that identity theft was
either imminent or in process. The following audit protocols have
proven useful in guarding against identity theft:
1. Periodic credit report examinations seeking inconsistencies.
2. Investigating sudden resignations from staff, advisors and/or closely related contractors.
3. Tracking delayed or missing bank/investment information.
4. Yearly background investigations on staff or others with access to sensitive personal and business information.
5. Improving key control accountability, including document control protocols within residences or offices.
6. Implementing controls on accessibility to financial, insurance and medical records at the respective offices.
7.
Implementing mail-screening protocols designed to detect "red flags,"
such as brochures from resorts never attended or from financial
institutions never associated with.
 Avoiding Identity Theft
Avoiding Identity Theft
For
the affluent, the place to start is in securing all their
communications as well as doing data classification to determine what
needs to be protected. A few communications points that should be
examined for security protocols include laptops, all computers,
blackberry/PDA and cellular or satellite communications. Each and every
phone system that is used between their estates and their corporate
facilities must be examined for compromise. We work hard to educate our
affluent clients to be attentive to the information they share. We ask
them to think about who would want to be listening to their
conversations and what information may be gleaned from those
conversations. All e-mail communications should be scrutinized, and
encrypted wherever possible. Many encryption technologies are
commercially available today in the form of hardware- or software-based
encryption. These technologies, left unprotected, could easily lead to
identity theft, liquidation of bank accounts and leaking of business
intellectual property.
Compromise of corporate and personal
communications for information is a significant threat today. We
regularly see situations where the cyber troller uses the information
not only to loot bank accounts but also for blackmail, as well as
facilitating the kidnapping of children because of exposed travel
plans.
In the event an individual's identity has been stolen, deploying the required containment and recovery procedures are critical. The following steps should be strongly considered:
- Step 1: The affluent family should instruct, in writing, all financial institutions: A freeze should be placed on all transactions. The only transactions that can be implemented require in-person verification from the principals, where two forms of government-approved identification are shown and one of them includes an up-to-date picture.
- Experian: 1-888-397-3742
- Equifax: 1-800-525-6285
- TransUnion: 1-800-680-7289
- Step 3: The affluent should immediately craft written instructions to close the accounts, preferably through legal counsel, with all lenders where fraudulent accounts have been opened. This needs to be followed up by telephone calls with the respective security departments advising them of the theft and requesting formal dispute documents for all charges made illegally. If, and it's usually the case, they request supporting documentation, only provide copies and retain the originals.
- Step 4: The local police department should be contacted and a police report should be filed. The affluent should be prepared to provide them with copies of all supporting documents. They should also retain the case number and determine who will be handling the case for follow-up. Once a copy of the police report is provided, it is submitted to each lending institution involved in the matter. This is often best accomplished through legal counsel.
- Step 5: The affluent should also file a complaint with the Federal Trade Commission (1-877-438-4338), as they can communicate the complaint to a variety of agencies for additional action.